- 入门指南
- 最佳实践
- 租户
- 注册表
- Cloud Robots
- Automation Suite 机器人
- 文件夹上下文
- 流程
- 作业
- Apps
- 触发器
- 日志
- 监控
- 索引
- 队列
- 资产
- 连接
- 业务规则
- 存储桶
- MCP 服务器
- Orchestrator 测试
- 资源目录服务
- 集成
- 故障排除

Orchestrator 用户指南
Managing credential proxies
您可以为自己的自定义凭据存储创建和管理代理,从而单独控制凭据的安全性。
代理类型
您可以在以下两种类型之间进行选择:
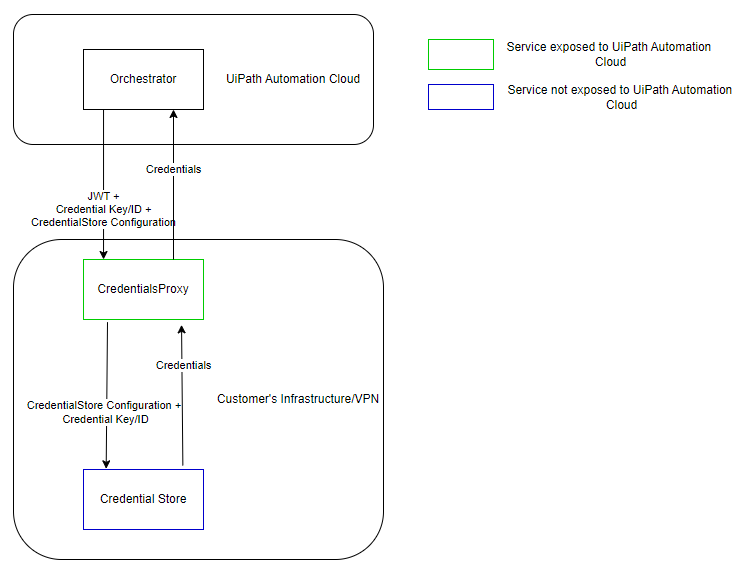
- 已连接代理(由 Orchestrator 管理)
- 当机器人请求凭据时,Orchestrator 将从代理检索凭据,并将其传递给机器人。
图 1. 连接代理架构
- 断开连接的代理(由代理服务管理) - 当机器人请求凭据时,会直接从代理检索凭据,而无需通过 Orchestrator。此类型仅与 23.10 及更高版本的 Robot 兼容。
图 2. 已断开的代理架构 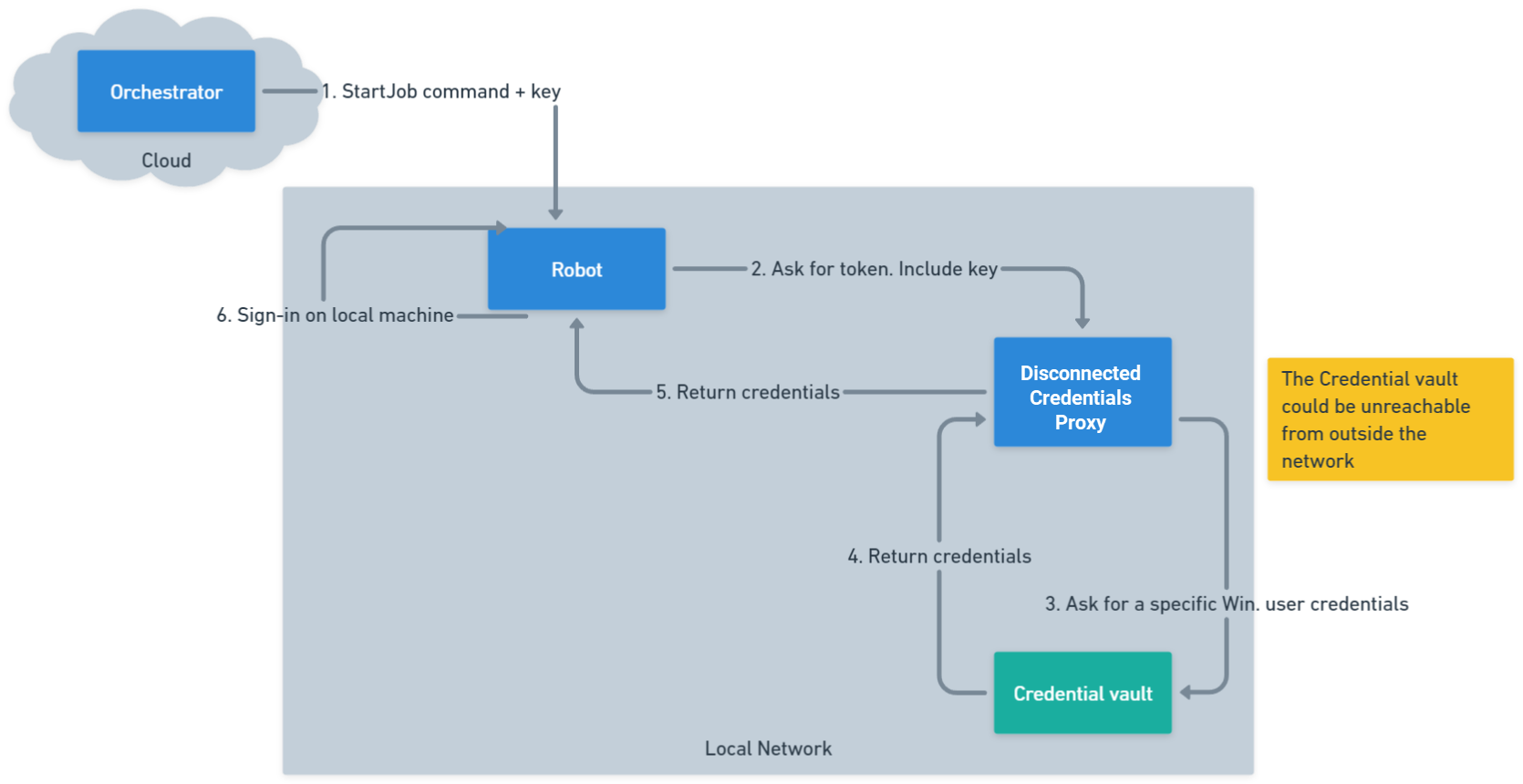
- 仅当您订阅企业版 - 高级许可计划时,才可以使用已断开连接的 Credentials Proxy。
- 如果要检索断开连接的代理凭据,则需要使用以下最低版本:2.0.1(针对代理)和 24.3(针对系统活动包)。
断开连接设置
Orchestrator Credentials Proxy 的断开连接工作方式与连接设置类似,但存在一些关键区别。
在 appsettings.json 文件中指定代理应以断开连接模式启动。要执行此操作,请在 AppSettings 下为参数 CredentialsProxyType 设置 Disconnected 值。
这将告诉代理在启动时以不同的方式执行操作,并从 appsettings.json 文件中读取其安全存储配置。如果参数缺失或值不同,代理将以其连接模式启动。
请在 appsettings.json 文件中指定代理应以断开连接模式启动。要执行此操作,请在 AppSettings 下为 CredentialsProxyType 参数设置 Disconnected 值。
{
...
"AppSettings": {
...
"CredentialsProxyType": "Disconnected",
...
}
}
{
...
"AppSettings": {
...
"CredentialsProxyType": "Disconnected",
...
}
}
这将告诉代理在启动时以不同的方式执行操作,并从appsettings.json文件中读取其安全存储配置。如果参数缺失或值不同,代理将以其连接模式启动。
安全存储配置
每个配置条目必须包含:
- 键: 链接存储时在 Orchestrator 中使用的唯一标识符。此参数在配置列表中必须是唯一的
- 类型:安全存储的类型(例如 Azure Key Vault、BeyondTrust、CyberArk、HashiCorp 保险库、InMemory 等)。
- 上下文:安全存储实施所需的数据,因存储类型而异。
选中以下安全存储配置示例:
{
...
"AppSettings": {
...
"SecureStoreConfigurations": [
{
"Key": "SecureStoreKey1",
"Type": "AzureKeyVault (read only)",
"Context": {
"KeyVaultUri": "{someUri}",
"DirectoryId": "{someDirectoryId}",
"ClientId": "{someClientId}",
"ClientSecret": "{someClientSecret}"
}
},
{
"Key": "SecureStoreKey2",
"Type": "BeyondTrust Password Safe - Managed Accounts",
"Context": {
"Hostname": "{someHost}",
"APIRegistrationKey": "{someApiKey}",
"APIRunAsUsername": "{someApiUsername}",
"DefaultManagedSystemName": "",
"SystemAccountDelimiter": "/",
"ManagedAccountType": "system"
}
},
{
"Key": "InMemoryKey1",
"Type": "InMemorySecureStore",
"Context": {
}
}
]
...
}
}
{
...
"AppSettings": {
...
"SecureStoreConfigurations": [
{
"Key": "SecureStoreKey1",
"Type": "AzureKeyVault (read only)",
"Context": {
"KeyVaultUri": "{someUri}",
"DirectoryId": "{someDirectoryId}",
"ClientId": "{someClientId}",
"ClientSecret": "{someClientSecret}"
}
},
{
"Key": "SecureStoreKey2",
"Type": "BeyondTrust Password Safe - Managed Accounts",
"Context": {
"Hostname": "{someHost}",
"APIRegistrationKey": "{someApiKey}",
"APIRunAsUsername": "{someApiUsername}",
"DefaultManagedSystemName": "",
"SystemAccountDelimiter": "/",
"ManagedAccountType": "system"
}
},
{
"Key": "InMemoryKey1",
"Type": "InMemorySecureStore",
"Context": {
}
}
]
...
}
}
SecureStoreConfigurations参数是一个配置数组,因此您可以根据需要使用任意数量的配置。只要Key值唯一,就支持相同类型的多个配置。
启动验证
在断开连接模式下运行时,代理会在启动时执行验证:
- 验证
appsettings.json中是否存在所需的配置 - 验证在
SecureStoreConfigurations中未找到重复的密钥。 - 确认所有
Type值都有效。 - 验证保险库连接(
ValidateContextAsync对每个商店进行调用)。
代理级设置
某些安全凭据存储需要主机级配置,需要在appsettings.Production.json中指定:
- CyberArk :必须在
AppSettings下定义CLIPasswordSDKExePath、UsePowerShellCLI和AdditionalAllowedCharacters等设置。{ // ... "AppSettings": { "Plugins.SecureStores.CyberArk.CLIPasswordSDKExePath": "D:\\SomePath\\CLIPasswordSDK.exe", // ... } // ... }{ // ... "AppSettings": { "Plugins.SecureStores.CyberArk.CLIPasswordSDKExePath": "D:\\SomePath\\CLIPasswordSDK.exe", // ... } // ... } - CyberArkCCP :可能需要
Plugins.SecureStores.CyberArkCCP.KeyStorageFlags = "MachineKeySet"。{ // ... "AppSettings": { "Plugins.SecureStores.CyberArkCCP.KeyStorageFlags": "MachineKeySet", // ... } // ... }{ // ... "AppSettings": { "Plugins.SecureStores.CyberArkCCP.KeyStorageFlags": "MachineKeySet", // ... } // ... }
配置测试示例
查看以下实际 appsettings.Production.json 示例。
在对 appsettings.Production.json 文件进行任何更改之前,确保创建原始文件的备份。这使您能够在设置期间出现问题时轻松恢复初始配置或比较更改。
示例 1:基本
使用 BeyondTrust 和 Azure 密钥保险库 进行配置:
{
"Jwt": {
"Keys": [
"<YourKey>"
]
},
"AppSettings": {
"CredentialsProxyType": "Disconnected",
"SecureStoreConfigurations": [
{
"Key": "SecureStoreKey3",
"Type": "BeyondTrust Password Safe - Team Passwords",
"Context": {
"Hostname": "<Hostname",
"APIRegistrationKey": "<APIRegistrationKey",
"APIRunAsUsername": "<Username>",
"FolderPathPrefix": "/", // default is "/", but it can be changed to anything
"FolderPasswordDelimiter": "/" // default is "/", but it can be changed to anything
}
}
]
}
}
{
"Jwt": {
"Keys": [
"<YourKey>"
]
},
"AppSettings": {
"CredentialsProxyType": "Disconnected",
"SecureStoreConfigurations": [
{
"Key": "SecureStoreKey3",
"Type": "BeyondTrust Password Safe - Team Passwords",
"Context": {
"Hostname": "<Hostname",
"APIRegistrationKey": "<APIRegistrationKey",
"APIRunAsUsername": "<Username>",
"FolderPathPrefix": "/", // default is "/", but it can be changed to anything
"FolderPasswordDelimiter": "/" // default is "/", but it can be changed to anything
}
}
]
}
}
示例 2:额外日志和多个配置
包括多个保险库和高级记录。
{
"Logging": {
"LogLevel": {
"Default": "Trace",
"Microsoft": "Warning",
"Microsoft.Hosting.Lifetime": "Information",
"Microsoft.AspNetCore.HttpLogging.HttpLoggingMiddleware": "Information"
}
},
"Jwt": {
"Keys": [ "<YourKey>" ]
},
"AppSettings": {
"Plugins.SecureStores": "UiPath.Orchestrator.CyberArk.dll;UiPath.Orchestrator.AzureKeyVault.SecureStore.dll;UiPath.Orchestrator.SecureStore.CyberArkCCP.dll;UiPath.Orchestrator.SecureStore.HashiCorpVault.dll;UiPath.Orchestrator.SecureStore.ThycoticSecretServer.dll;UiPath.Orchestrator.SecureStore.BeyondTrust.dll;UiPath.Orchestrator.SecureStore.AWSSecretsManager.dll",
"UseInMemorySecureStore": "true",
"CredentialsProxyType": "Disconnected",
"SecureStoreConfigurations": [
// AzureKeyVault owned by <username>; contact for more info
// Robot externalName: "<name>"
// The expected value of this secret is "<name>"
{
"Key": "SecureStoreKey1",
"Type": "AzureKeyVault (read only)",
"Context": {
"KeyVaultUri": "<VaultURL>",
"DirectoryId": "<DirectoryID>",
"ClientId": "<ClientID>",
"ClientSecret": "<ClientSecret>"
}
},
// In case this fails, check our internal documentation on checking if BeyondTrust is down
// <InternalDocsURL>
// Robot externalName: "<ExternalName>"
{
"Key": "SecureStoreKey2",
"Type": "BeyondTrust Password Safe - Managed Accounts",
"Context": {
"Hostname": "<Hostname>",
"APIRegistrationKey": "<APIRegistrationKey>",
"APIRunAsUsername": "<Username>",
"DefaultManagedSystemName": "",
"SystemAccountDelimiter": "/",
"ManagedAccountType": "system"
}
},
// In case this fails, check our internal documentation on checking if BeyondTrust is down
// <InternalDocsURL>
// Robot externalName: "<ExternalName>"
{
"Key": "SecureStoreKey3",
"Type": "BeyondTrust Password Safe - Team Passwords",
"Context": {
"Hostname": "<Hostname>",
"APIRegistrationKey": "<APIRegistrationKey>",
"APIRunAsUsername": "<Username>",
"FolderPathPrefix": "/", // default is "/", but it can be changed to anything
"FolderPasswordDelimiter": "/" // default is "/", but it can be changed to anything
}
},
{
// asset external name: Operating System-WinDomain
// password: <password>
"Key": "SecureStoreKey1",
"Type": "CyberArk Conjur Cloud (read only)",
"Context": {
"ServiceUrl": "<ServiceURL>",
"LoginName": "<LoginName>",
"ApiKey": "<APIKey>",
"VariableIdPrefix": "data/vault/Safe"
}
},
// Must have an empty context
// No values on startup; should add values using the endpoints before trying trying to get anything
{
"Key": "InMemoryKey1",
"Type": "InMemorySecureStore",
"Context": {
}
}
]
}
}
{
"Logging": {
"LogLevel": {
"Default": "Trace",
"Microsoft": "Warning",
"Microsoft.Hosting.Lifetime": "Information",
"Microsoft.AspNetCore.HttpLogging.HttpLoggingMiddleware": "Information"
}
},
"Jwt": {
"Keys": [ "<YourKey>" ]
},
"AppSettings": {
"Plugins.SecureStores": "UiPath.Orchestrator.CyberArk.dll;UiPath.Orchestrator.AzureKeyVault.SecureStore.dll;UiPath.Orchestrator.SecureStore.CyberArkCCP.dll;UiPath.Orchestrator.SecureStore.HashiCorpVault.dll;UiPath.Orchestrator.SecureStore.ThycoticSecretServer.dll;UiPath.Orchestrator.SecureStore.BeyondTrust.dll;UiPath.Orchestrator.SecureStore.AWSSecretsManager.dll",
"UseInMemorySecureStore": "true",
"CredentialsProxyType": "Disconnected",
"SecureStoreConfigurations": [
// AzureKeyVault owned by <username>; contact for more info
// Robot externalName: "<name>"
// The expected value of this secret is "<name>"
{
"Key": "SecureStoreKey1",
"Type": "AzureKeyVault (read only)",
"Context": {
"KeyVaultUri": "<VaultURL>",
"DirectoryId": "<DirectoryID>",
"ClientId": "<ClientID>",
"ClientSecret": "<ClientSecret>"
}
},
// In case this fails, check our internal documentation on checking if BeyondTrust is down
// <InternalDocsURL>
// Robot externalName: "<ExternalName>"
{
"Key": "SecureStoreKey2",
"Type": "BeyondTrust Password Safe - Managed Accounts",
"Context": {
"Hostname": "<Hostname>",
"APIRegistrationKey": "<APIRegistrationKey>",
"APIRunAsUsername": "<Username>",
"DefaultManagedSystemName": "",
"SystemAccountDelimiter": "/",
"ManagedAccountType": "system"
}
},
// In case this fails, check our internal documentation on checking if BeyondTrust is down
// <InternalDocsURL>
// Robot externalName: "<ExternalName>"
{
"Key": "SecureStoreKey3",
"Type": "BeyondTrust Password Safe - Team Passwords",
"Context": {
"Hostname": "<Hostname>",
"APIRegistrationKey": "<APIRegistrationKey>",
"APIRunAsUsername": "<Username>",
"FolderPathPrefix": "/", // default is "/", but it can be changed to anything
"FolderPasswordDelimiter": "/" // default is "/", but it can be changed to anything
}
},
{
// asset external name: Operating System-WinDomain
// password: <password>
"Key": "SecureStoreKey1",
"Type": "CyberArk Conjur Cloud (read only)",
"Context": {
"ServiceUrl": "<ServiceURL>",
"LoginName": "<LoginName>",
"ApiKey": "<APIKey>",
"VariableIdPrefix": "data/vault/Safe"
}
},
// Must have an empty context
// No values on startup; should add values using the endpoints before trying trying to get anything
{
"Key": "InMemoryKey1",
"Type": "InMemorySecureStore",
"Context": {
}
}
]
}
}
示例 3:自定义日志路径和 InMemoryStore
{
"NLog": {
"throwConfigExceptions": true,
"targets": {
"logfile": {
"type": "File",
"maxArchiveFiles": 180,
"fileName": "<FileName>",
"layout": "${longdate} ${logger} ${message}${onexception:${newline}${exception:maxInnerExceptionLevel=10:format=shortType,message,stacktrace:separator=*:innerExceptionSeparator=
	}}"
}
},
"rules": [
{
"logger": "*",
"minLevel": "Information",
"writeTo": "logconsole,logfile,eventLog"
}
]
},
"Logging": {
"LogLevel": {
"Default": "Information",
"Microsoft.AspNetCore": "Warning"
}
},
"Jwt": {
"Keys": [
"<YourKey>"
]
},
"AppSettings": {
"Plugins.SecureStores": "UiPath.Orchestrator.CyberArk.dll;UiPath.Orchestrator.AzureKeyVault.SecureStore.dll;UiPath.Orchestrator.SecureStore.CyberArkCCP.dll;UiPath.Orchestrator.SecureStore.CyberArkConjur.dll;UiPath.Orchestrator.SecureStore.HashiCorpVault.dll;UiPath.Orchestrator.SecureStore.ThycoticSecretServer.dll;UiPath.Orchestrator.SecureStore.BeyondTrust.dll;UiPath.Orchestrator.SecureStore.AWSSecretsManager.dll",
"UseInMemorySecureStore": "true",
"CredentialsProxyType": "Disconnected",
"SecureStoreConfigurations": [
{
"Key": "InMemoryKey1",
"Type": "InMemorySecureStore",
"Context": {}
}
]
}
}
{
"NLog": {
"throwConfigExceptions": true,
"targets": {
"logfile": {
"type": "File",
"maxArchiveFiles": 180,
"fileName": "<FileName>",
"layout": "${longdate} ${logger} ${message}${onexception:${newline}${exception:maxInnerExceptionLevel=10:format=shortType,message,stacktrace:separator=*:innerExceptionSeparator=
	}}"
}
},
"rules": [
{
"logger": "*",
"minLevel": "Information",
"writeTo": "logconsole,logfile,eventLog"
}
]
},
"Logging": {
"LogLevel": {
"Default": "Information",
"Microsoft.AspNetCore": "Warning"
}
},
"Jwt": {
"Keys": [
"<YourKey>"
]
},
"AppSettings": {
"Plugins.SecureStores": "UiPath.Orchestrator.CyberArk.dll;UiPath.Orchestrator.AzureKeyVault.SecureStore.dll;UiPath.Orchestrator.SecureStore.CyberArkCCP.dll;UiPath.Orchestrator.SecureStore.CyberArkConjur.dll;UiPath.Orchestrator.SecureStore.HashiCorpVault.dll;UiPath.Orchestrator.SecureStore.ThycoticSecretServer.dll;UiPath.Orchestrator.SecureStore.BeyondTrust.dll;UiPath.Orchestrator.SecureStore.AWSSecretsManager.dll",
"UseInMemorySecureStore": "true",
"CredentialsProxyType": "Disconnected",
"SecureStoreConfigurations": [
{
"Key": "InMemoryKey1",
"Type": "InMemorySecureStore",
"Context": {}
}
]
}
}
创建 Credentials Proxy
安装Orchestrator Credentials Proxy 后,您可以创建一个自定义代理,用于保存自定义凭据存储。
图 3. “添加 Credentials Proxy”页面 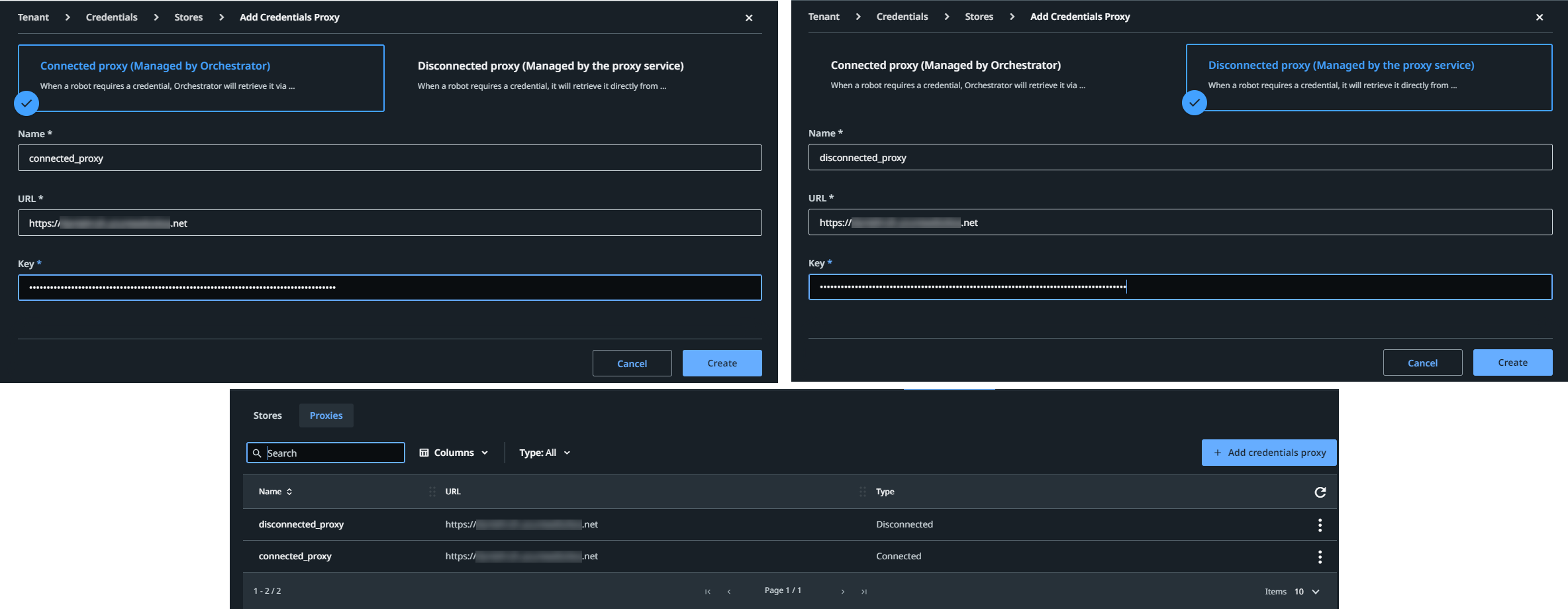
为完成此操作,请按照以下步骤操作:
- 在租户级别,选择“凭据” > “代理” > “添加 Credentials Proxy”。此时将显示“添加 Credentials Proxy”窗口。
- 选择“已连接的代理(由 Orchestrator 管理)”或“已断开的代理(由代理服务管理)”。
- 为代理添加名称。
- 添加与 Orchestrator Credentials Proxy 设置中包含的虚拟机相关的 URL。
- 添加密钥。
对于已连接的代理,根据安装方法的不同,这是由 .msi 安装程序生成的密钥,或 Jwt:Keys 参数保存的密钥。
对于断开连接的代理,此密钥必须已存在于已断开连接的代理的某个本地配置文件中。
您在步骤 4 和 5 中提供的信息在 Orchestrator 与包含自定义凭据存储插件的安装之间创建链接。
- 选择“创建”。
然后,您可以按如下方式添加所需的存储:
- 在租户级别,选择“凭据” > “存储” > “添加凭据存储”,以添加凭据存储。
- 在“代理”列表中,选择刚刚创建的代理。
- 从“类型”列表中,选择插件定义的第三方凭据存储。
- 提供与代理本地配置文件中的配置密钥匹配的配置密钥。
备注:
对于断开连接的设置,请确保 Orchestrator 中使用的密钥与代理配置文件中定义的密钥一致。 对于已连接的设置,Orchestrator 会自动管理配置。
Editing a credentials proxy
To edit a proxy, click More Actions > Edit. The Edit Credentials Proxy page is displayed, allowing you to change the name, URL, or key as needed.
正在删除 Credentials Proxy
要删除代理,请选择“更多操作”>“移除”。如果所选代理正在使用中,将出现一个警告对话框,列出将受影响的机器人和资产的数量。选择“是”以确认移除,或选择“否”以中止。
图 4. “代理”选项卡